
Table of Contents
- 1 Cybersecurity Analysts: Your Cortisol Is the Zero-Day Exploit in Your Own Biology
- 1.1 1. SIEM Alert Fatigue and the Amygdala Hijack
- 1.2 Visualizing the Threat: The Biological Kill Chain
- 1.3 2. HPA Axis Dysregulation: The Kernel Panic of the Endocrine System
- 1.4 3. The Caffeine Exploit: Amplifying the Cortisol Attack Vector
- 1.5 4. Diminished Cognitive Fidelity: The Liability of Burnout
- 1.6 5. The Biological Patch: A Remediation Protocol for Hypervigilance
- 1.7 Conclusion: Engineer Your Biological Defenses
Cybersecurity Analysts: Your Cortisol Is the Zero-Day Exploit in Your Own Biology
In the world of cybersecurity and threat hunting, a zero-day vulnerability is the ultimate nightmare scenario: an unpatched exploit running silently in the system’s kernel, possessing administrative privileges, operating undetected by standard telemetry, and causing systemic damage that will only be discovered after the exfiltration is complete. The defensive architecture is actively being subverted by an internal element it trusts. In 2026, the cybersecurity industry is facing an epidemic that perfectly mirrors this technical phenomenon, but the target infrastructure is the biological hardware of the analysts themselves. Your cortisol is the zero-day.
Incident response and SIEM (Security Information and Event Management) monitoring are not just ‘stressful’ jobs. They require maintaining a sustained state of hypervigilance that human biology evolved to only deploy in short, life-or-death bursts. When you are sifting through thousands of alerts, hunting lateral movement across network logs, and carrying the psychological weight of a potential multi-million dollar breach, your body does not distinguish between a digital threat and a physical predator. Post-pandemic occupational health research indicates that the modern Security Operations Center (SOC) operates as a continuous crisis environment. According to recent mental health studies targeting the cybersecurity sector, the psychological strain experienced by tier-2 and tier-3 analysts now closely parallels that of front-line emergency workers. The cost of this ‘always-on’ mentality is biological degradation at the cellular level, driven entirely by dysregulated cortisol.
1. SIEM Alert Fatigue and the Amygdala Hijack
The standard SIEM dashboard is an inadvertent machine designed to perpetually trigger the human sympathetic nervous system. Alert fatigue is cited as the number one cause of burnout in security teams, but the psychological label obscures the biochemical reality. Every flashing red priority alert, regardless of whether it is a false positive or an active ransomware deployment, forces a micro-activation of the amygdala. The brain’s threat-detection center overrides the prefrontal cortex, ordering the immediate release of adrenaline and cortisol into the bloodstream.
In a healthy nervous system, the resolution of a threat brings a parasympathetic ‘rest and digest’ response. The cortisol clears, heart rate variability (HRV) recovers, and the system resets. For a cybersecurity analyst triaging 500+ alerts per shift, there is no threat resolution. The sheer volume of telemetry creates a continuous, low-level drip of stress hormones. The brain remains in a perpetual state of hypervigilance. Over time, the baseline amygdala activation threshold lowers. The result is chronic, systemic inflammation and an inability to downregulate the nervous system even when the shift is over. This is why you feel the phantom vibration of a PagerDuty alert while trying to fall asleep. By monitoring your sleep architecture, you can track the exact degree to which your nervous system is failing to return to baseline.
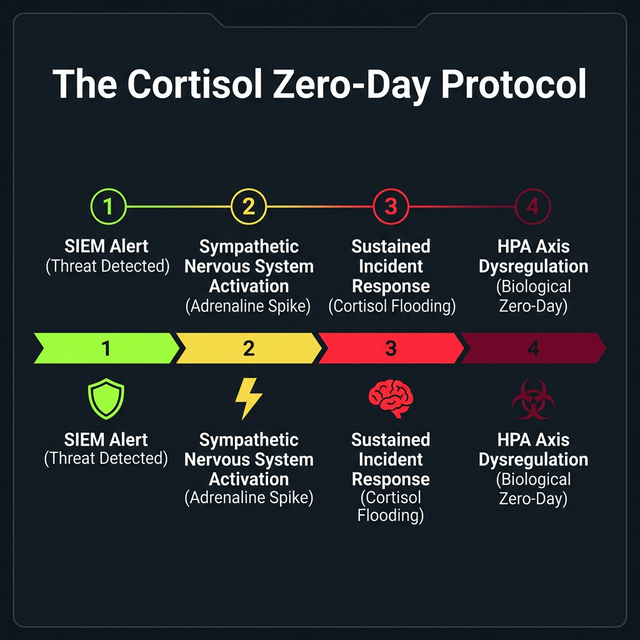
Visualizing the Threat: The Biological Kill Chain
The progression from targeted incident response to systemic physiological failure follows a predictable sequence, analogous to a cyber kill chain. Understanding this biological zero-day protocol is the first step in engineering a defense.
2. HPA Axis Dysregulation: The Kernel Panic of the Endocrine System
The Hypothalamic-Pituitary-Adrenal (HPA) axis is the master control plane for your body’s stress response. When cortisol is chronically elevated due to sustained incident response deployments, a negative feedback loop fails. Initially, the adrenal glands hypertrophy (grow larger) to meet the constant demand for cortisol. However, as months of high-adrenaline threat hunting turn into years, the system fatigues. The HPA axis becomes desensitized, resulting in a state colloquially known as ‘adrenal fatigue’—though clinically recognized as HPA axis dysregulation.
This dysregulation manifests as profound, unshakeable brain fog. The prefrontal cortex—the area of your brain responsible for logic, complex packet analysis, and strategic incident containment—actually shrinks under the neurotoxic load of prolonged cortisol exposure. When your HPA axis crashes, your ability to perform deep cognitive work is fundamentally compromised. You begin making basic errors, missing clear instances of privilege escalation, and losing the intuitive thread during complex threat hunts. It is a biological kernel panic, and no amount of energy drinks will patch the vulnerability.
⚡ Editor’s Choice: The Genius Wave (Theta Audio Protocol)
A 7-minute daily audio program engineered by neuroscientists. It uses binaural beats and isochronic tones to stimulate Theta brainwaves (4-7 Hz), shifting the brain out of a stressed Beta state.
Best For: Loss of focus and creative problem-solving blocks during complex, multi-hour coding sprints.
- Activates neuroplasticity for faster problem-solving
- Requires only 7 minutes daily (fits easily into a developer’s morning routine)
- Non-chemical alternative to caffeine stacking
Telemetry Comparison: The Nervous System vs. Network Security
| Biological State | Neurological Impact | Cybersecurity Analogy |
|---|---|---|
| Baseline (Parasympathetic) | Optimal prefrontal cortex function, clear logic | Nominal operations, zero active alerts |
| Acute Stress (Sympathetic) | Elevated focus, narrow attention window | Active incident response, targeted threat hunting |
| Chronic Cortisol Load | Memory impairment, emotional exhaustion | SIEM alert fatigue, logs dropping due to volume |
| HPA Axis Dysregulation | Severe brain fog, inability to process complex data | Complete kernel panic, firewall failure |
| Systemic Inflammation | Immune suppression, metabolic disruption | Unpatched zero-day executing arbitrary code |
3. The Caffeine Exploit: Amplifying the Cortisol Attack Vector
To combat the exhaustion of HPA axis dysregulation, analysts instinctively turn to stimulants. Caffeine is the industry-standard mitigation script for fatigue, but in the context of chronic stress, it acts as a force multiplier for the zero-day exploit. Caffeine works by blocking adenosine receptors, preventing the neurochemical signal for sleepiness from registering. However, it also stimulates the adrenal glands to release even more adrenaline and cortisol. When a hypervigilant analyst consumes 600mg to 800mg of caffeine to survive a 12-hour incident response shift, they are pouring liquid stress hormones onto an already overloaded HPA axis.
Furthermore, the half-life of caffeine ensures that these elevated cortisol levels persist well into the night, destroying the restorative deep sleep required to repair the prefrontal cortex. The cycle becomes self-perpetuating: poor sleep leads to increased dependency on stimulants, which further degrades the oral microbiome and elevates cortisol. It is an unmitigated attack vector. Standardizing your daily caffeine intake calculations is critical, but true remediation requires targeted supplementation that supports the adrenal system rather than whipping it into further exhaustion.
4. Diminished Cognitive Fidelity: The Liability of Burnout
In 2026, the fear of personal liability in the event of a breach is a significant vector of psychological strain. CISOs and lead analysts are intensely aware that missed threats can result in career-ending consequences. Yet, the paradox is that the chronic stress generated by this fear is actively eroding the cognitive fidelity required to prevent the breach. Studies published in leading neuroscience journals confirm that chronic stress shrinks the hippocampus—the brain’s memory center. This means that past threat patterns, IOCs (Indicators of Compromise), and architectural nuances of the network become harder to retrieve under pressure.
When an analyst experiences extreme burnout, their threat-hunting methodology degrades from a proactive, hypothesis-driven approach to a reactive, checklist-oriented survival mode. They stop looking for the anomalies hidden in the noise and focus only on clearing the most glaring red alerts from the dashboard. This cognitive tunnel vision is exactly what Advanced Persistent Threats (APTs) rely on to maintain persistence in a network. To protect the network, you must prioritize the integrity of your own biological processing units. Routine metabolic checks using the Modern BMI tracking tool provide a baseline, but cognitive sharpness requires deliberate recovery protocols.
5. The Biological Patch: A Remediation Protocol for Hypervigilance
You cannot patch a zero-day vulnerability by simply restarting the server, and you cannot reverse cortisol dysregulation with a weekend of sleep catch-up. Remediation requires an intentional, structural overhaul of your biological configuration. The first step is implementing “Vagal Brake” techniques. The vagus nerve is the primary countermeasure to the sympathetic nervous system. Engaging the vagus nerve through specific, physiological sighs (double inhale, long exhale) immediately forces a downregulation of the amygdala. This must be scheduled and executed as rigidly as a firewall rule update after every major incident triage.
Secondly, analysts must decouple from the “always-on” asynchronous communication loop. Continuous partial attention to Slack or Teams channels prevents the nervous system from ever dropping below a baseline level of arousal. Implement hard physical boundaries: no devices in the bedroom, and a mandatory 90-minute digital air-gap before attempting sleep. Finally, addressing the physical cost of seated hypervigilance requires offsetting the metabolic damage of sedentary tension. Your muscles hold the physical memory of a 12-hour triage. Regular somatic release or targeted resistance training is necessary to process the accumulated stress hormones out of the peripheral tissues.
Conclusion: Engineer Your Biological Defenses
The cybersecurity industry trains its professionals to execute complex defense-in-depth strategies to secure digital perimeters, yet provides zero training on how to secure the internal biological perimeter of the human operators running the systems. A Security Operations Center is only as resilient as the neurobiology of the analysts sitting at the monitors.
Your cortisol zero-day is actively executing. Every hour spent in hypervigilance without a corresponding parasympathetic recovery protocol is an hour where your body is silently incurring technical debt. The consequences of this biological breach are far more permanent than any ransomware attack. It is time to audit your internal systems, patch the vulnerabilities in your neurochemical baseline, and build a biological architecture capable of surviving the realities of modern incident response. Defense starts internally.
Disclaimer: The content on TheHealthyTechPro is for educational purposes only and does not constitute medical advice. Consult a qualified healthcare professional before making health-related decisions. This article contains affiliate links; we may earn a commission at no additional cost to you, which supports our ability to continue producing high-quality, research-backed content.